139: Crowdstrike Q1, Ackman & PSTH + UMG, E-Commerce, Cloud Security Misalignment, FBI & DOJ on Ransomware, TerraPower, AMD 3D, and The Expanse's User Interfaces
"death by a thousand cuts is still death"
I am not responsible for actions of the imaginary version of me you have inside your head.
—John Scalzi
🙈 🙉 Before the pandemic, a thing on my “to try” list was floating around in a sensory deprivation tank for a while, but COVID-19 put those plans on hold.
Just to see how it feels, and what my brain will come up with when there’s little inbound signal.
I found a couple places nearby — I think it’ll soon be time to put those plans on the docket.
Friend-of-the-show Jerry Capital seems to have had good experiences with it. Curious if you’ve ever tried it and what the experience was like?
🛀 Ok, hear me out. The Truman Show, but set in 2021, and Truman has a smart phone that is entirely compromised by the TV show people.
🤔 If you understand 100% of what you’re reading or listening to, are you really learning much?
I don’t mean “100%” literally, but some amount that is probably closer to it than the optimal point for growth and learning (whatever that point is — it varies by person and by topic, I’m sure).
I think we tend to play it too safe on average (I include myself in this).
I have to often remind myself to step outside of my comfort zone, even if sometimes it doesn’t work out… Because once in a while, when it does work, it’s how I make the best discoveries and grow the most.
f.ex. Sometimes I listen to fairly technical podcasts about things I don’t know much — like Peter Attia and Tom Dayspring on lipidology or Omega Tau on tokamak nuclear fusion reactors — and I grok way less than 100% of what they’re saying.
But jumping in the deep end does make you learn a lot faster than staying in the shallow part of the pool, and I tend to find that the next time I’m listening to something on topic, I now understand maybe 5% more, or 10%, and so one.
And maybe if I re-listen to the same podcast a while later, I find that I now understand much more of it, either because I learned things elsewhere in the meantime, or I had time to digest it — our brains run all kinds of background processes that we have little visibility into — or I can focus on the bigger picture the second time around because I’m not just trying to keep up with the moments-to-moments beats.
It’s a bit like learning a new language: Some stuff you pick up over time from context and sheer repetition, other stuff you have to pause and look up in the dictionary/on Wikipedia. But with some effort and active-listening, you can make a lot of progress.
Anyway, all this to say that I encourage you to get out of your comfort zone when it comes to the things you read and listen to.
Try to learn about a whole new field today, flex that beginner’s mind.
Gödel, Escher, Bach was no doubt one of the most challenging books I read in my early 20s, but it was also one of the most mind-expanding and rewarding (looking back, I realize it was probably a big inspiration, seeing Hofstadter do complex, serious stuff in such a playful and personal way).
h/t to friend-of-the-show and supporter (💚 🥃) Luis Sanchez for the email conversation that sparked me thinking about this
🤬 I watch watching the video of a virtual “salon” discussion that Anna Gát did with Jimmy Wales (co-founder of Wikipedia with Larry Sanger, who too often gets overlooked despite his importance to the creation of one of humanity’s great institutions), and Anna said something about when she checks the wiki page of a new author, she jumps to 'criticism', and if there's none, that's a bad sign ("nobody cared enough... mediocre ideas", something like that).
Nice heuristic. Indifference as a signal.
Great ideas/art rarely leaves people indifferent, or make everyone happy.
🎶 There’s an audio gear company called “Schiit”. It’s both a brilliant and terrible name, and it tickles me. Thanks to my friend M-A.AC for reminding me of them.
They have a sexy website with good copywriting in the product descriptions. If you want to learn about how to do a good product website, this isn’t a bad place to learn.
Sadly, their Vidar amp that would fit my needs for my office upgrade (which I described in the intro of edition #132) is twice the price of the NAD model I was looking at.
Still fun to look at their stuff:
⛵️🏝 In the intro of edition #137 I used a shore metaphor about knowledge.
Thanks to reader Luo Ji for reminding me of a similar metaphor I had written a year ago. I kinda like it, so I’m going to repost it here:
The more you know, the more you realize you don't know much.
Every new discovery allows you to peer at more unknown things at the edge of your knowledge.
Another way to see it: A small circle of knowledge has a short coastline with the unknown. A larger circle, a longer coastline.
So the paradox is, the more you learn, the dumber you feel. But that's better than the alternative, so keep going.
And if you want to feel really dumb, be more of a generalist.
Then you can feel like you don't know anything about history / physics / math / engineering / music / film / writing / biology / nutrition / etc rather than just not know anything in one field, like finance.
💚 🥃 If you like this project and want to see it continue, the way to make that happen is to become a supporter.
It’s 77 cents per edition and takes 19 seconds (or 3 on mobile) to sign up. If it’s not worth WAY WAY more tan 77 cents to you, why are you even reading?
Investing & Business
Clarification
I realize it may seem like all I’m interested in are these exciting high-growth software companies.
I want to make it clear that I don’t make investment recommendations here, I write about what I find interesting.
That’s the filter that stuff goes through. Most of the time, there’s not much interesting to write about, say, Charter’s latest quarter.
People pay their cable bills, they buy back their stock. Tom Rutledge talks about churn and bundling and insourcing and growing faster by holding back on flexing pricing power. End of story.The companies that are highlighted more often here just are more interesting and fast-moving.
That doesn’t necessarily make them better investments, but it certainly makes for better writing (and, I hope, reading).
Crowdstrike Q1 Highlights
With that out of the way, let’s look at Crowdstrike’s Q1:
As we extend the platform beyond core protection, we are seeing strong momentum in cloud workloads, IT operations and our expansion into dev ops.
This is an important part of what they do: Keep expanding to new areas, through new modules that can be implemented through the same, lightweight agent (that’s the piece of software that sits on the endpoints being protected and gives Crowdstrike a view into what is going on there, captures the data that is analyzed centrally, and gives the ability to intervene at-a-distance when there are problems).
You can’t just look at what they do today and think “how is that thing going to be doing in 10 years?”, because in a decade they’ll be doing a bunch more things.
Just since IPO, they’ve shown this with the addition of 9 new modules (iirc) and two acquisitions that added new functionality/technologies (Preempt and Humio).
our leadership is recognized by both customers and industry analysts such as Gartner and Forrester. Our growing brand has become the cybersecurity gold standard [...]
We believe the rapid expansion of our partner ecosystem also demonstrates our growing leadership position. As we discussed in our webinar in April, our partner-sourced ARR grew 86% in fiscal year 2021. Partners naturally gravitate to market leaders as it helps them bring in new customers.
This reminds me of something Everbridge’s former CFO said:
If you're buying a bulletproof vest as a policeman, would you buy the $50 cheaper one?It’s kind of a version of the previous-era “nobody got fired for buying IBM”.
If Crowdstrike is really becoming the new leader in the space, the gold-standard, that comes with a lot of benefits when it comes to customer acquisition/retention and the ability to do win-win partnerships (like with Zscaler), because buying security products is kind of like buying insurance: You hope you won’t have to use it, and that if you do, that it won’t be too bad and everything will go well.
So if Crowdstrike can be that company that reduces career risk for those making security decisions at all kinds, that’ll provide them a nice tailwind that may not be available to competitors with duller brands.
Threat actors are well resourced and becoming more sophisticated. At the same time, ransomware-as-a-service sites are making it easier for even novice e-criminals to run successful and lucrative campaigns, which is contributing to the proliferation of ransomware activity.
Y’know how the internet is making everything easier? Anyone can be a podcaster, a publisher, learn how to code, how to repair a car, etc..?
Well, same applies to black-hat hacking and the creation of support communities and organizations that facilitate it (it’s especially easy when you have safe-haven places like Russia…).
Our 2020 CrowdStrike Global Security Attitude Survey revealed that more than half of organizations surveyed worldwide had suffered a ransomware attack within the previous 12 months.
More than half! Of course, most are pretty small, but still, death by a thousand cuts is still death.
Falcon achieved 100% detection coverage in all 20 steps of the MITRE ATT&CK evaluations, showcasing the effectiveness of our platform. And lastly, the Falcon platform achieved 100% protection rate in the AV-Comparatives business real-world protection test for the March-April 2021 period and the highest AAA rating in the Q1 enterprise endpoint protection evaluation from independent testing organization, SE Labs.
The mousetrap seems to catch mice.
our partnership with Zscaler continues to deepen as we both invest in our technology and commercial relationship. We announced multiple new technology integrations with Zscaler this quarter and are also excited to report that they are now a CrowdStrike customer. [...]
we've set up compensation structures between the 2 organizations, where both sales teams are incented to help each other out
Feels like a kind of company bromance going on here.
They’re indeed very complimentary and don’t have much overlap, and if they can get each other’s salesforce to help sell some of the other’s stuff and integrate the products so they work well together (reducing churn for both), it can be quite win-win for them, both in the salesforce leverage, but also in more effectively competing together against more integrated competing solutions.
In the last quarter, We more than doubled ARR from our newly launched cloud workload modules. We are rapidly scaling our overall cloud footprint with greater than 20% of all servers we protect being in the public cloud.
This is the cloud workload opportunity that Kurtz was extremely effusive about at their investor day. He basically seems to see it as almost endless greenfield:
in general, it's a greenfield opportunity in cloud. There's not a lot of competitors and existing technologies we have to displace.
Here’s Kurtz doing a glove slap to Microsoft:
Our next customer win is with a Fortune 150 multinational manufacturing company. After trying to deploy Microsoft Defender for over a year, they found themselves frustrated with the level of complexity and the cumbersome agents, resulting in less than 1/3 of their endpoints protected.
On top of that, the recent zero-day Microsoft Exchange vulnerability has exposed them to risk of a potential breach, and they would have to wait months before Microsoft could deliver a patch to fully resolve the issue.
This is when they turned to CrowdStrike.
With our single lightweight agent that doesn't require a reboot, this new customer found Falcon easy to deploy, fast and effective. As a result, they purchased 5 modules and deployed globally in a matter of weeks.
🔥
They also do a customer story like this from someone moving away from a SentinelOne deployment (they just filed their S-1, haven’t had much time to look yet), and it’s pretty savage (“Frustrated at the lack of scalability, need for manual updates and continuous crashes with SentinelOne”).
I’ll skip it in the interest of time, but you can find it in the transcript if you’re curious.
On the size of the market:
11,000 [customers] is fantastic, but when you look at other competitors over the many, many years, they've had hundreds of thousands. So we certainly think we can be in that arena in the future.
Not only is the security pie still growing (and growing in new directions like cloud workloads, zero trust, etc), but they’ve also only got a pretty small slice.
Q: your thoughts on what inning you think you're in, in regards to taking share from legacy vendors.
A: I think we're still in the early innings, maybe second inning in terms of our ability to continue to take share.
Pro tip: Always use baseball metaphors, because innings are a more granular answer than in other sports where games are split into fewer time-segments.
Ackman & PSTH
Friend-of-the-show and supporter (💚🥃) Andrew Walker has an interesting speculation on what happened with Ackman’s hyper-hyped SPAC:
I think it’s pretty clear what happened with PSTH. Remember that Ackman filed to raise PSTH in late May 2020 and they IPO’d in July 2020. At the time, Ackman was on the heels of having absolutely nailed the COVID trade (buying credit swaps when the market wasn’t prepped for COVID, then selling them at a mammoth profit at the peak of fear). While the market wasn’t in full panic mode in late May 2020, the future was still incredibly uncertain; plenty of people still thought we were going to go into a depression from COVID, and many people thought getting a vaccine by the end of 2021 would be optimistic. So Ackman raised that money at an absolute high, thinking he could go after a unicorn that had been hit by COVID (AirBNB was his first target and hits that thesis perfectly). But then the market rallied furiously, and cheap cash was available in near unlimited quantities to basically every company. No one wanted to take Ackman’s money; there was cheaper money with less strings attached floating around everywhere.
The Directional Arrow of E-Commerce
Part of the story of e-commerce for the last 25 years has been that there is literally no category that people will not buy online, but you need to work out the right experience.
Science & Technology
Security Expert Bruce Schneier on Cloud Security Misalignment
The problem is one of economics. On the surface, it might seem that competition between cloud companies gives them an incentive to invest in their users’ security. But several market failures get in the way of that ideal. First, security is largely an externality for these cloud companies, because the losses due to data breaches are largely borne by their users. As long as a cloud provider isn’t losing customers by the droves — which generally doesn’t happen after a security incident — it is incentivized to underinvest in security. Additionally, data shows that investors don’t punish the cloud service companies either: Stock price dips after a public security breach are both small and temporary.
Second, public information about cloud security generally doesn’t share the design trade-offs involved in building these cloud services or provide much transparency about the resulting risks. While cloud companies have to publicly disclose copious amounts of security design and operational information, it can be impossible for consumers to understand which threats the cloud services are taking into account, and how. This lack of understanding makes it hard to assess a cloud service’s overall security. As a result, customers and users aren’t able to differentiate between secure and insecure services, so they don’t base their buying and use decisions on it.
Third, cybersecurity is complex — and even more complex when the cloud is involved. For a customer like a company or government agency, the security dependencies of various cloud and on-premises network systems and services can be subtle and hard to map out.
This is an excerpt from a longer post.
👮🏻♂️👮🏻♂️ U.S. D.O.J. & F.B.I. on Ransomware Attacks
The U.S. Department of Justice is elevating investigations of ransomware attacks to a similar priority as terrorism [...]
Internal guidance sent on Thursday to U.S. attorney’s offices across the country said information about ransomware investigations in the field should be centrally coordinated with a recently created task force in Washington.
WSJ:
FBI Director Christopher Wray said the agency was investigating about 100 different types of ransomware, many tracing back to hackers in Russia, and compared the current spate of cyberattacks with the challenge posed by the Sept. 11, 2001, terrorist attacks. [...]
senior Biden administration officials have characterized ransomware as an urgent national-security threat and said they are looking at ways to disrupt the criminal ecosystem that supports the booming industry. [...]
“The scale of this problem is one that I think the country has to come to terms with,” [FBI Director Christopher Wray] said.
TerraPower & Berkshire Energy to build Natrium Nuclear Demonstration Plant
The project features a 345 megawatt sodium-cooled fast reactor with molten salt-based energy storage that could boost the system’s power output to 500MW during peak power demand. TerraPower said last year that the plants would cost about $1bn. [...]
Chris Levesque, TerraPower’s president and chief executive, said the demonstration plant would take about seven years to build (Source)
This will be located in Wyoming on the site of a coal plant that is being decommissioned (how symbolic is that?).
Natrium basically means salt.
I’m not expert, but from what I know, I really like the liquid-fluoride thorium reactor (LFTR) design because of the very high passive security (ie. you have to actively keep the reaction running, and if anything happens to change that balance, it automatically stops the reaction.. Even under total power loss, the cryo-plug at the bottom of the salt reservoir just melts and the whole thing empties itself and just can’t keep a reaction going. It’s a very clever design).
If you want to know more about LFTRs, I recall learning a bunch about it from this site a few years ago (but haven’t checked recently):
Terrapower made this site on their design:
This Terrapower design is using uranium (afaik), which is probably a way to keep costs down, since a lot more R&D has gone into uranium reactors over the decades (thorium was overlooked mostly because you can’t make bombs out of it, and early nuclear countries wanted that military tech tree).
‘AMD triples Zen 3 CPU cache using 3D stacking technology’
This is neat. There’s a whole other dimension that is starting to be explored in the semi world:
AMD CEO Lisa Su showed off the company's next big performance play—3D stacked chiplets, allowing the company to triple the amount of L3 cache on its flagship Zen 3 CPUs.
The technology is just what it sounds like—a layer of SRAM cache sitting atop the Complex Core Die (CCD) of the CPU itself. Current Zen 3 architecture integrates 32MiB of L3 cache per eight-core chiplet—making 64MiB total for a 12- or 16-core chiplet like the Ryzen 9 5900X or 5950X. The new technology adds an additional 64MiB L3 cache on top of each chiplet's CCD, bonded with through-silicon vias (TSVs). [...]
Tripling the L3 cache on Ryzen 5000 allows performance gains under some workloads—particularly archive compression/decompression and gaming—similar to those seen with entire new CPU generations. [...]
AMD claims an average of 15 percent improved gaming performance with the new technology, ranging from a low of 4 percent for League of Legends to a high of 25 percent for Monster Hunter: World. (Source)
The Arts & History
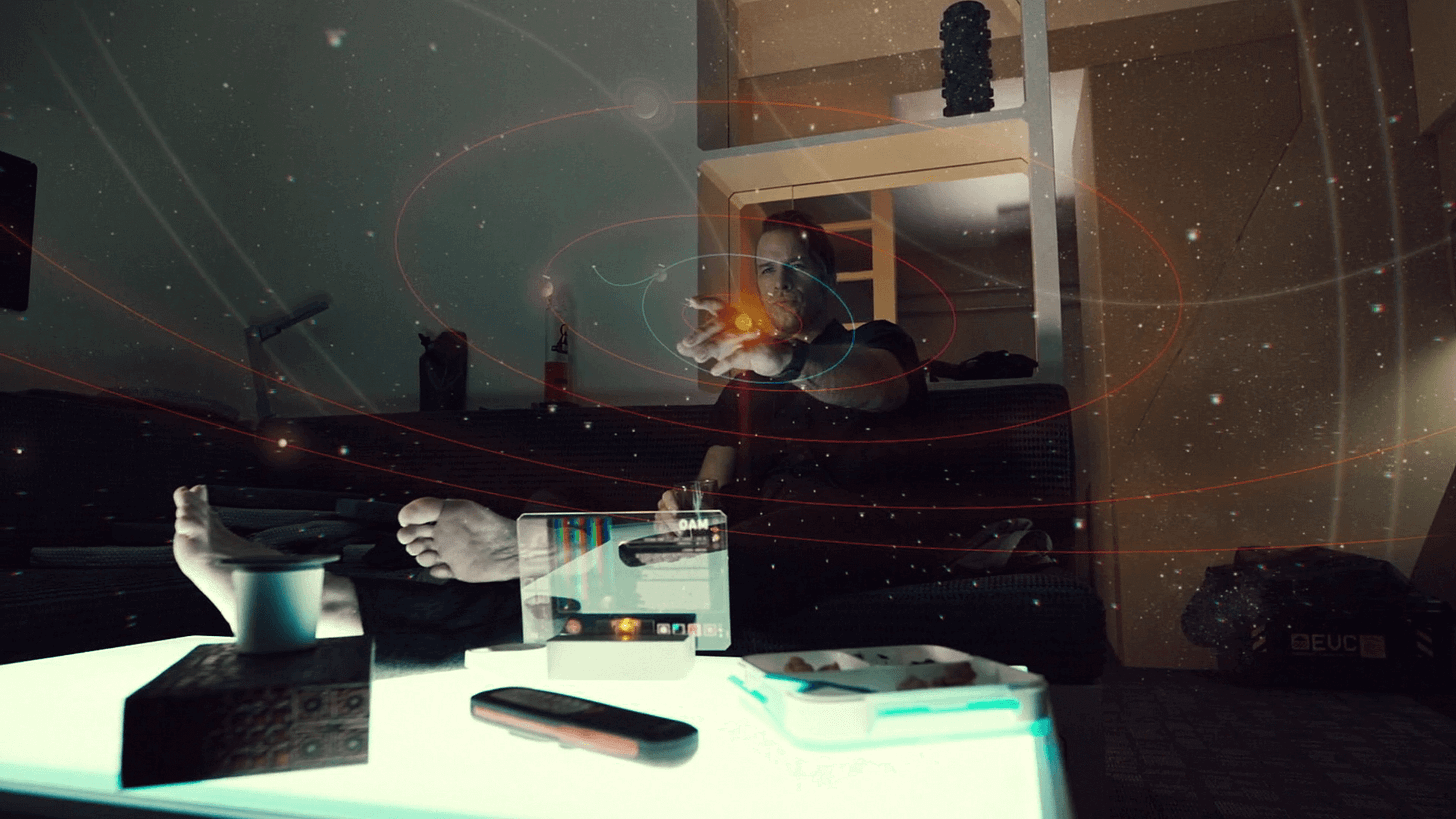
‘The Expanse UI Design’
Neat compilation of user-interface design from the sci-fi show ‘The Expanse’ (2015-?).
They look at how they designed holographic displays, mobile devices, touch screens, larger curved screens, and various utility displays around ships and buildings.
Then there’s a Q&A with Rhys Yorke, the motion graphics designer who worked on seasons 3 & 5 of the show.
I thought this detail was cool:
Q: Was the majority of the work done in post production or did the actors have interfaces on the screens in front of them?
A: The great thing about the Expanse was that the Production Designer, Toni Ianni, was keen on having real interfaces for the actors to interact with as much as possible. This meant that we had the opportunity to build functional interactive screens as well as screens that were triggered by on-set playback.